Attack Paths, Blast Radius, and the Graph That Connects Everything
Leonard Volling
May 6, 2026
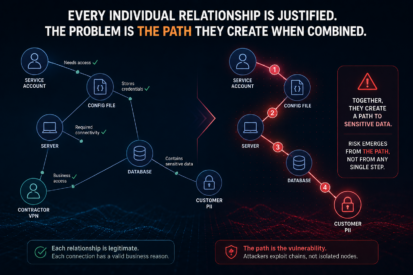
Security is not just a graph problem during investigation. It is a graph problem before, during, and after the breach. The previous post focused on w...
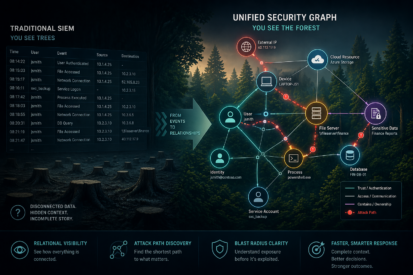
Why Your SIEM Shows You Trees When You Need to See the Forest
Leonard Volling
April 29, 2026
Security analysts spend their days staring at tables. Rows and columns of log entries, each one a discrete event frozen in time. User authenticated. ...
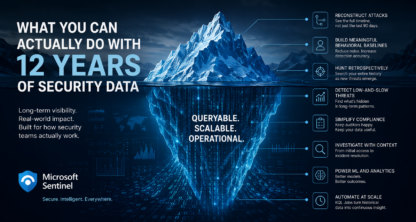
What You Can Actually Do With 12 Years of Security Data
Leonard Volling
April 15, 2026
Most security teams are operating with institutional amnesia. Not by choice, but by architecture. You keep 90 days of logs because that's what the bu...
The Real Cost of Security Visibility (And Why It's About to Change)
Leonard Volling
November 21, 2025
There's a conversation happening in every security operations center that nobody wants to have. It usually starts during budget planning, surfaces ag...
Microsoft Sentinel's Transformation: Why This Changes Everything for Security Operations
Leonard Volling
October 31, 2025
Did you catch Microsoft Secure on September 30, 2025? Have you seen What's new in Sentinel? Something fundamental just shifted in the security operat...
Deploying Microsoft Defender for Endpoint with CrowdStrike (or any EDR)
Charlie Smith
December 21, 2024
At LockBase Cyber, we work with organizations of varying sizes, industries, levels of sophistication, and maturity. In conversations about Microsoft ...